- Get link
- X
- Other Apps
In this post, we will be publishing On-Premise Exchange OWA to users to take advantages of Multifactor Authentication in Office 365.
One next screen login with the account with the Global admin privileges.
Next, create a "New Connector Group" name it as OWA and assigned the registered node to it, this will designate this node only for the OWA app.
Step 3:
In the next step, we will register our Application and publish it.
Click on "Configure an App", Give it a Name as you like, and type internal URL of the application, and select the Connector group we created and click Add.
In the Next Step, we will add the permissions for users.
go to "Enterprise Application", select the application we registered.
As we can see that the OWA opened with the app proxy default URL, Next we will rebrand it with the custom domain owa.lab365.in
Requirement:
Scenario:
User Mailbox is hosted on-premise, users can access the OWA over VPN or on the company network
Users are synced to Office 365 and have access to other o365 applications such as Sharepoint and MS teams etc.
Project requirement: Enabled OWA access over the internet using Azure App Proxy, Users will be able to access mail over OWA using Office 365. (https://portal.office.com/myapps) or (https://myapps.microsoft.com) or the direct URL (https://owa.lab365.in) which will proxy through Azure app.
Steps:
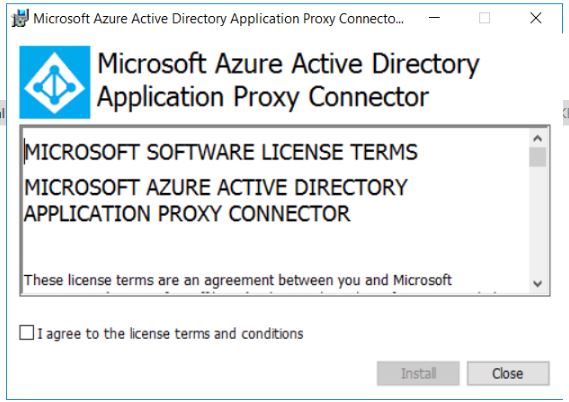
- Install Application Proxy Connector Server: need at least one, use multiple for redundancy
- Register the connector, needs to be done by the Global Admin
- Configure app
- Assign App to users
- Testing
- Branding External address (owa.lab365.in from default "owa-domain.msappproxy.net")
App proxy can be installed on the server from where it can resolve the internal application URL, in the LAB I have installed the app proxy on Exchange and LAB DC, in production you may wish to install it on a separate server.
One next screen login with the account with the Global admin privileges.
You should see the Setup Successful completion screen if all goes well.
Log in the Azure Portal and go to "Application Proxy", you should see the registered server and "Active".
Next, create a "New Connector Group" name it as OWA and assigned the registered node to it, this will designate this node only for the OWA app.
Step 3:
In the next step, we will register our Application and publish it.
Click on "Configure an App", Give it a Name as you like, and type internal URL of the application, and select the Connector group we created and click Add.
In the Next Step, we will add the permissions for users.
go to "Enterprise Application", select the application we registered.
Next, Under "manage" select the "Users and Groups" and add the permissions for the Users of the Groups.
Once added, login to the URL "https://myapps.microsoft.com" and should see the OWA_LAB365 app published.
Open the app to test it, if all has gone well. you will be able to see the application loaded successfully.
As we can see that the OWA opened with the app proxy default URL, Next we will rebrand it with the custom domain owa.lab365.in
Requirement:
- Domain should be registered with office 365.
- Create a CNAME DNS record which points "owa-lab365.msappproxy.net" (Azure portal will show the prompt for this.)
- Need certificate in .pfx format.
once the requirement and completed select the domain from the dropdown and save to configuration.
Next, update the certificate.
Once done, you should be able to access the OWA using the external URL.
(Note: as I am in a lab environment so I skipped the last step to upload the certificate, so you may see the "Note Secure" in the screenshot below)
This completes my post on Publishing OWA using Azure App Proxy, where we learned to configure the azure app, granting access to users, and setting up custom domain URL. feel free to leave your comments and suggestions.
- Get link
- X
- Other Apps
Comments











Great article, thanks. I would like to have conditional access policies (CAP) managing OWA accessing the URL for Office 365 mailboxes. Is this possible? How?
ReplyDeleteYou can put the CAP on the published app.
DeleteNi
ReplyDelete